Effective Network Defense Strategies to Assure Service Continuity Under Collaborative Attacks Pdf
EFFECTIVE NETWORK PLANNING AND DEFENDING STRATEGIES TO MINIMIZE SERVICE COMPROMISED PROBABILITY UNDER MALICIOUS COLLABORATIVE ATTACKS Advisor: Professor Frank, Y. S. Lin Presented by Chi-Hsiang Chan
AGENDA Problem Description Mathematical Formulation
AGENDA Problem Description Mathematical Formulation
PROBLEM DESCRIPTION Network Survivability � Collaborative attack Commander Attacker group � Various defense mechanisms VMM IDS Dynamic topology reconfiguration Cloud security service
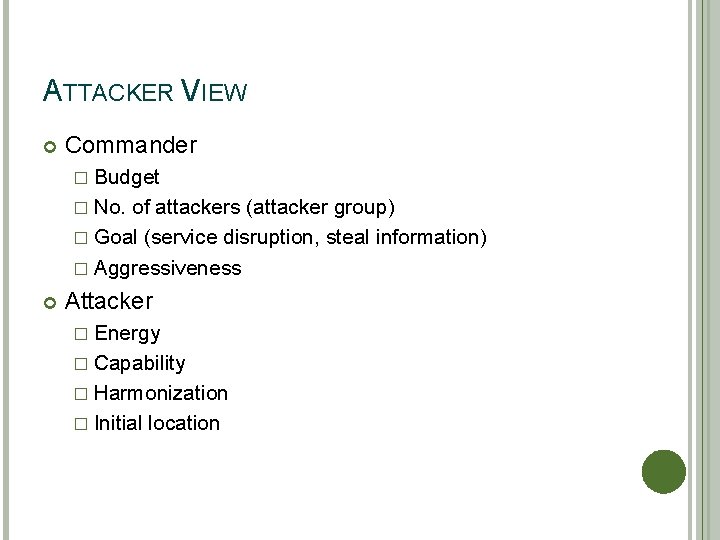
ATTACKER VIEW Commander � Budget � No. of attackers (attacker group) � Goal (service disruption, steal information) � Aggressiveness Attacker � Energy � Capability � Harmonization � Initial location
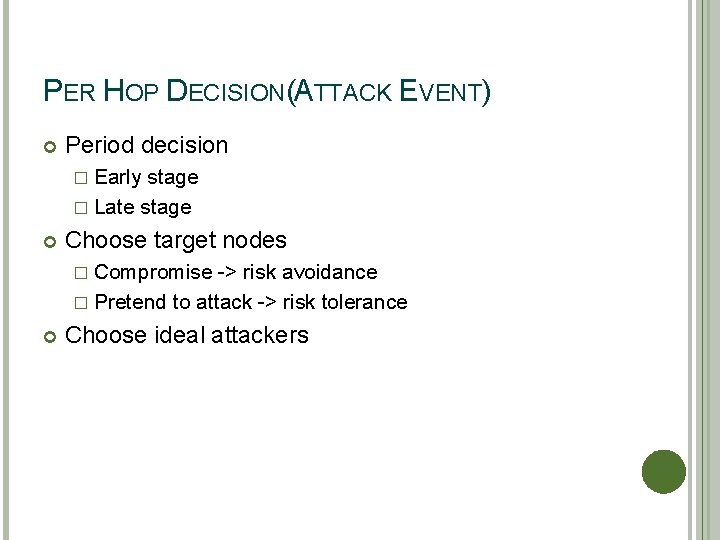
PER HOP DECISION(ATTACK EVENT) Period decision � Early stage � Late stage Choose target nodes � Compromise -> risk avoidance � Pretend to attack -> risk tolerance Choose ideal attackers
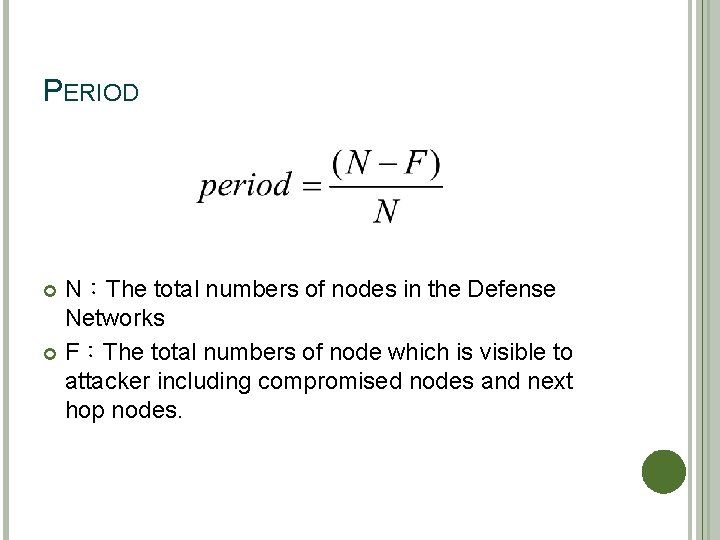
PERIOD N:The total numbers of nodes in the Defense Networks F:The total numbers of node which is visible to attacker including compromised nodes and next hop nodes.
PERIOD
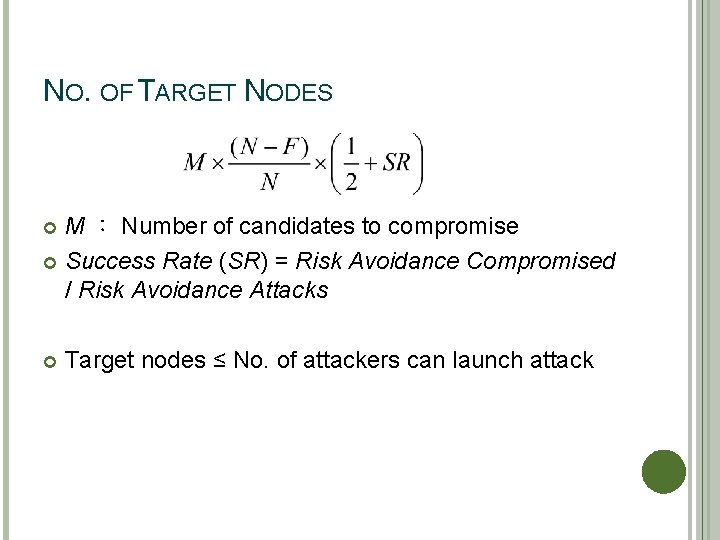
NO. OF TARGET NODES M : Number of candidates to compromise Success Rate (SR) = Risk Avoidance Compromised / Risk Avoidance Attacks Target nodes ≤ No. of attackers can launch attack
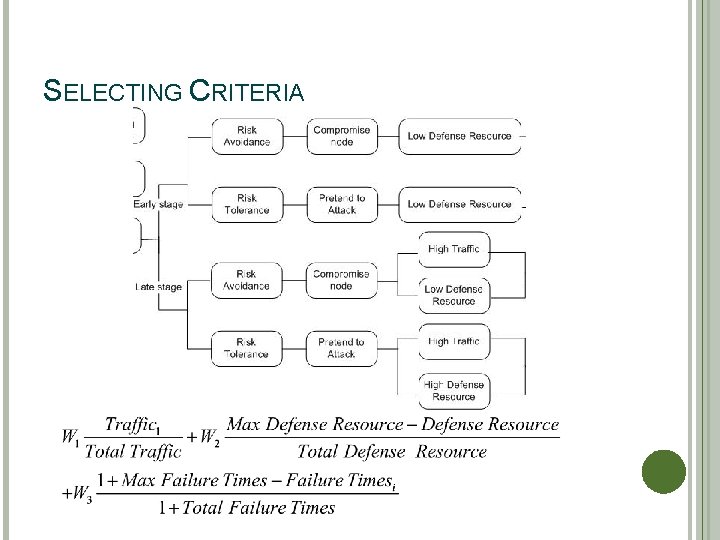
SELECTING CRITERIA
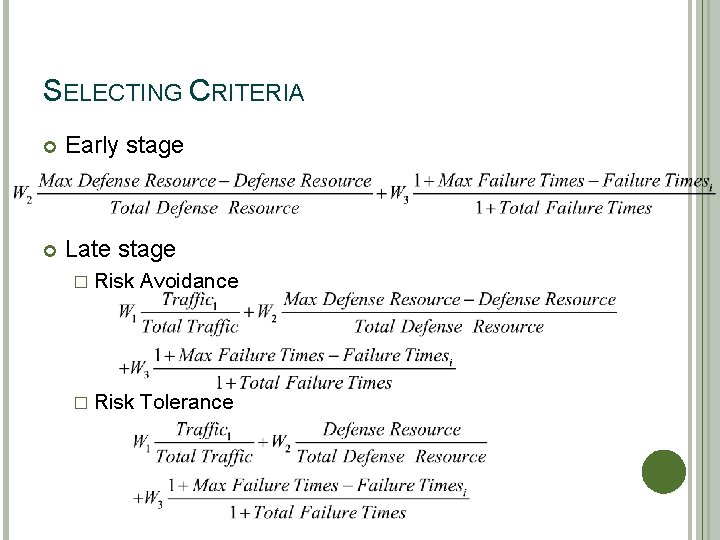
SELECTING CRITERIA Early stage Late stage � Risk Avoidance � Risk Tolerance
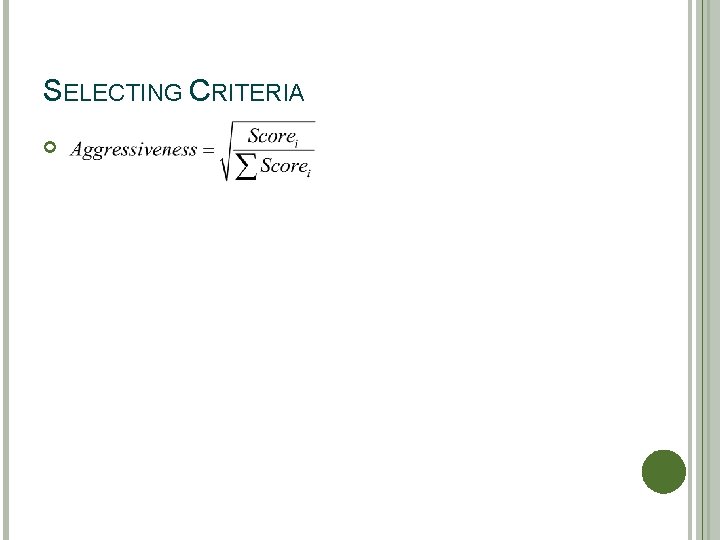
SELECTING CRITERIA
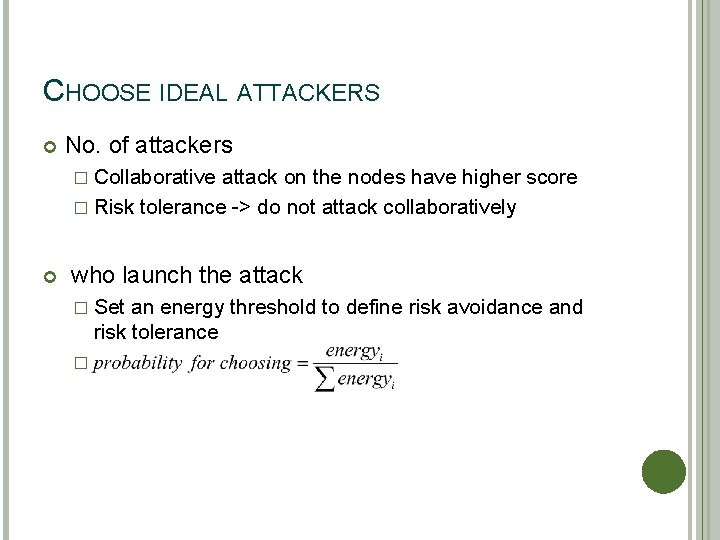
CHOOSE IDEAL ATTACKERS No. of attackers � Collaborative attack on the nodes have higher score � Risk tolerance -> do not attack collaboratively who launch the attack � Set an energy threshold to define risk avoidance and risk tolerance �
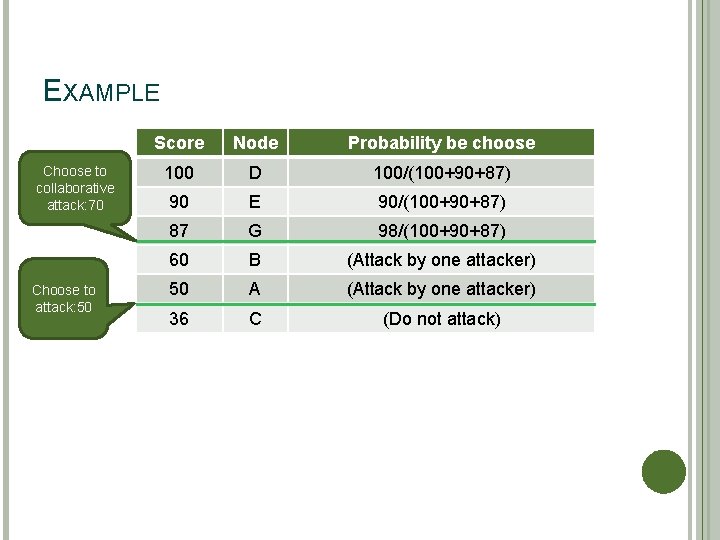
EXAMPLE Choose to collaborative attack: 70 Choose to attack: 50 Score Node Probability be choose 100 D 100/(100+90+87) 90 E 90/(100+90+87) 87 G 98/(100+90+87) 60 B (Attack by one attacker) 50 A (Attack by one attacker) 36 C (Do not attack)
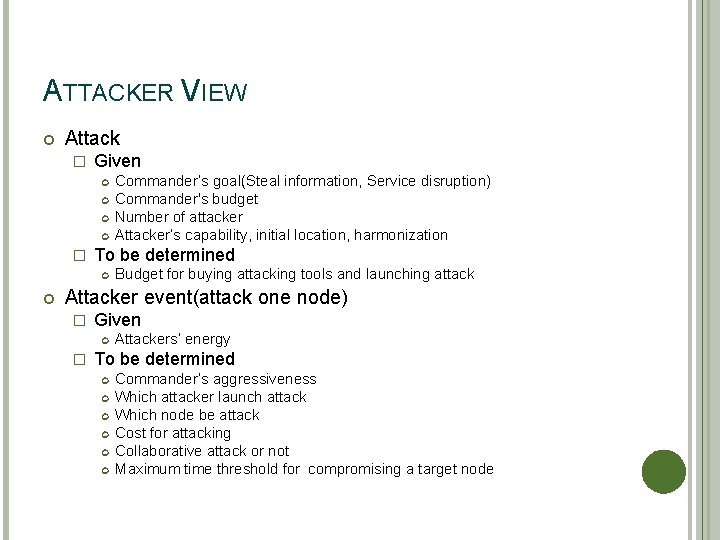
ATTACKER VIEW Attack � Given � To be determined Commander's goal(Steal information, Service disruption) Commander's budget Number of attacker Attacker's capability, initial location, harmonization Budget for buying attacking tools and launching attack Attacker event(attack one node) � Given � Attackers' energy To be determined Commander's aggressiveness Which attacker launch attack Which node be attack Cost for attacking Collaborative attack or not Maximum time threshold for compromising a target node
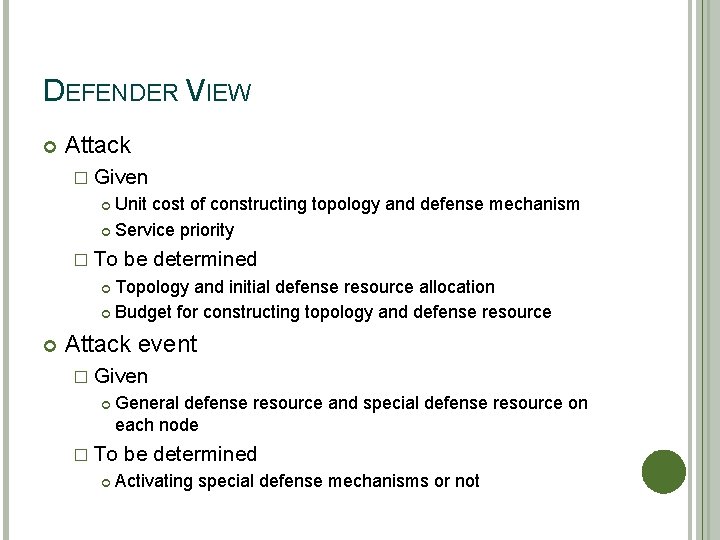
DEFENDER VIEW Attack � Given Unit cost of constructing topology and defense mechanism Service priority � To be determined Topology and initial defense resource allocation Budget for constructing topology and defense resource Attack event � Given General defense resource and special defense resource on each node � To be determined Activating special defense mechanisms or not
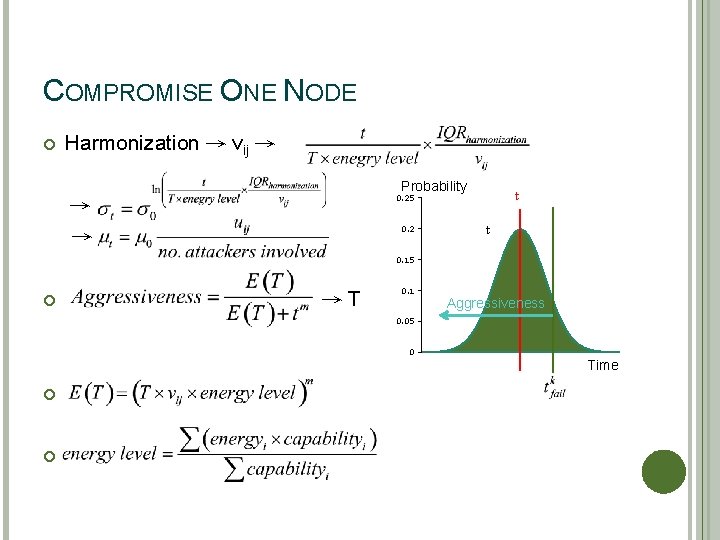
COMPROMISE ONE NODE Harmonization → vij → Probability t 0. 25 → → 0. 2 t 0. 15 →T 0. 1 Aggressiveness 0. 05 0 Time
AGENDA Problem Description Mathematical Formulation
MATHEMATICAL FORMULATION Objective � To minimize maximized service compromised probability Given � Attacker's and defender's total budget � Cost of construct topology and defending resource � Qo. S requirement To be determined � Attack and defense configuration � Budget spend on each defending mechanism
ASSUMPTIONS 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. All attack events are atomic operations. There are multiple core nodes and services in the network. Each core node can provide only one specific service. Each service has different weight, which is determined by the defender. There is an SOC with full control of the network. The defender has complete information of network and can allocate resources or adopt defense solutions by the SOC. Commanders have only incomplete information about the network. Only nodes with VMM-IPS have local defense function. Only nodes with VMM-IPS have signature request function. Only nodes with cloud security agent have cloud security function.
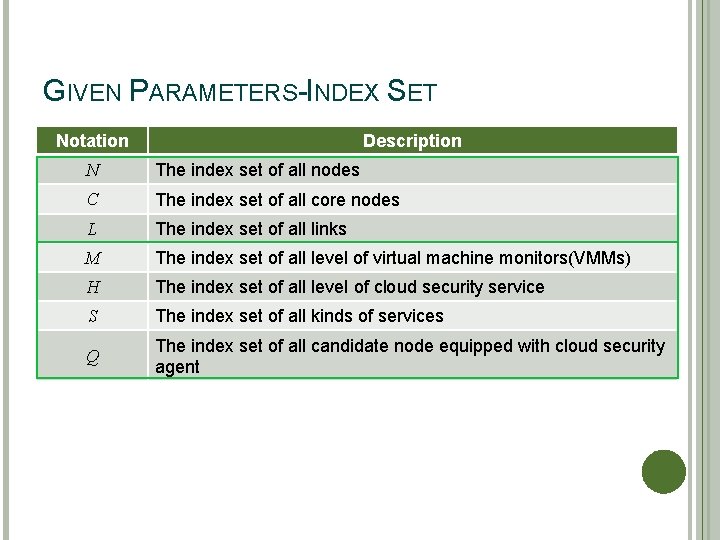
GIVEN PARAMETERS-INDEX SET Notation Description N The index set of all nodes C The index set of all core nodes L The index set of all links M The index set of all level of virtual machine monitors(VMMs) H The index set of all level of cloud security service S The index set of all kinds of services Q The index set of all candidate node equipped with cloud security agent
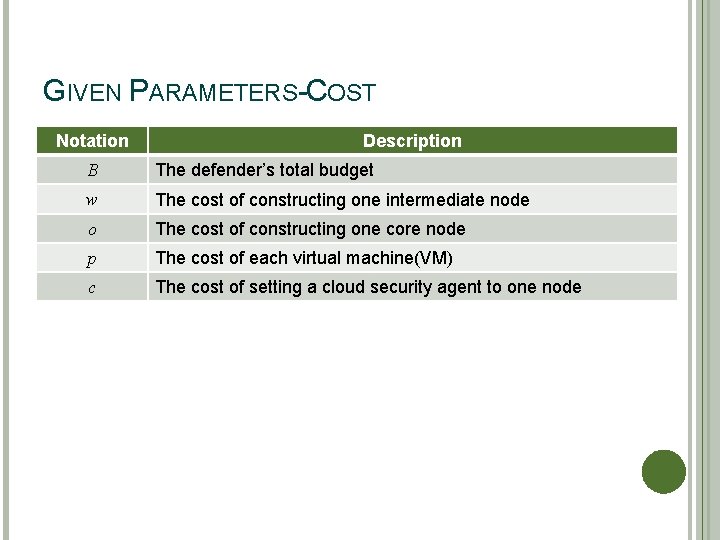
GIVEN PARAMETERS-COST Notation Description B The defender's total budget w The cost of constructing one intermediate node o The cost of constructing one core node p The cost of each virtual machine(VM) c The cost of setting a cloud security agent to one node
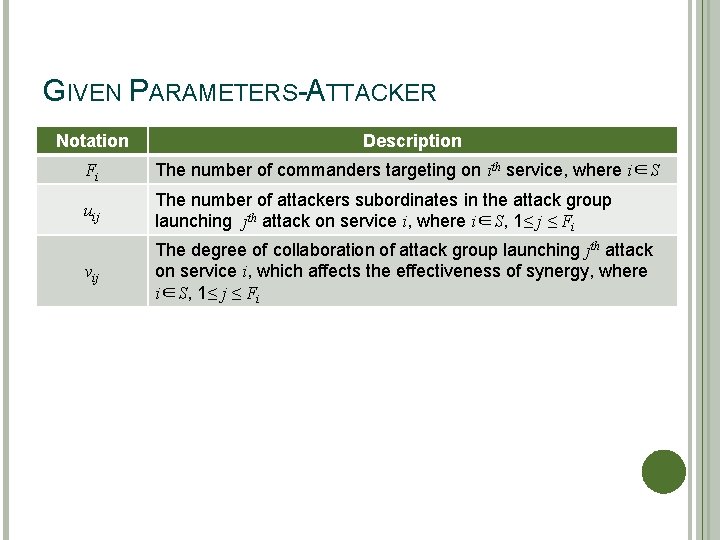
GIVEN PARAMETERS-ATTACKER Notation Description Fi The number of commanders targeting on ith service, where i∈S uij The number of attackers subordinates in the attack group launching jth attack on service i, where i∈S, 1≤ j ≤ Fi vij The degree of collaboration of attack group launching jth attack on service i, which affects the effectiveness of synergy, where i∈S, 1≤ j ≤ Fi
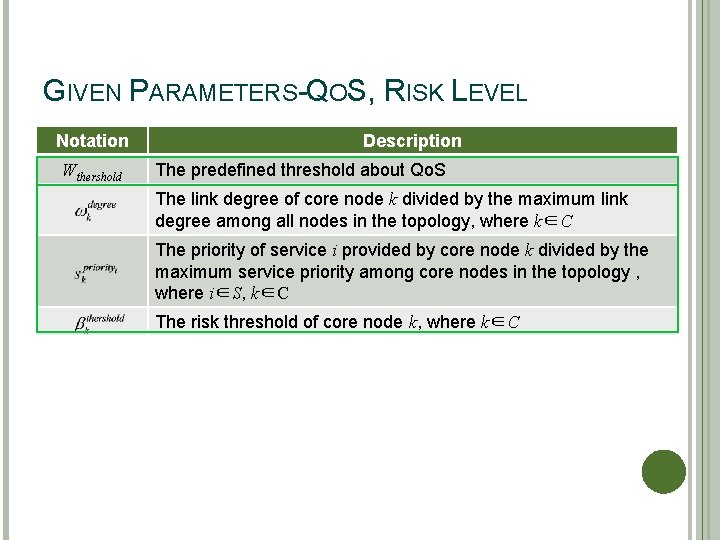
GIVEN PARAMETERS-QOS, RISK LEVEL Notation Wthershold Description The predefined threshold about Qo. S The link degree of core node k divided by the maximum link degree among all nodes in the topology, where k∈C The priority of service i provided by core node k divided by the maximum service priority among core nodes in the topology , where i∈S, k∈C The risk threshold of core node k, where k∈C
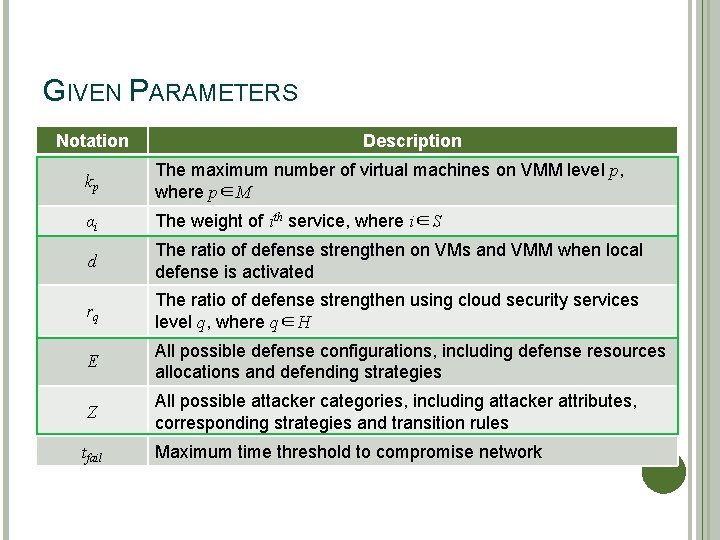
GIVEN PARAMETERS Notation The degree of collaboration Description of attack group The number of virtual machines on VMM level p, launching jthmaximum attack on service i, which affects the kp where p∈M effectiveness of synergy, where i∈S, 1≤ j ≤ Fi th αi The weight of i service, where i∈S d The ratio of defense strengthen on VMs and VMM when local defense is activated rq The ratio of defense strengthen using cloud security services level q, where q∈H E All possible defense configurations, including defense resources allocations and defending strategies Z All possible attacker categories, including attacker attributes, corresponding strategies and transition rules tfail Maximum time threshold to compromise network
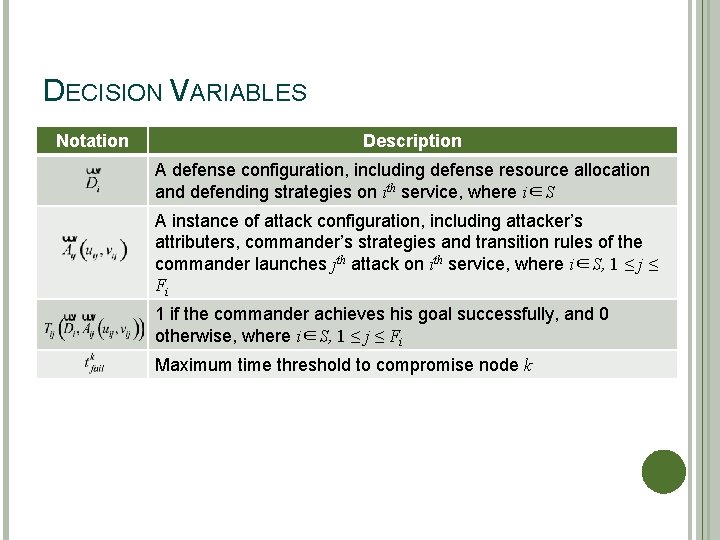
DECISION VARIABLES Notation Description A defense configuration, including defense resource allocation and defending strategies on ith service, where i∈S A instance of attack configuration, including attacker's attributers, commander's strategies and transition rules of the commander launches jth attack on ith service, where i∈S, 1 ≤ j ≤ Fi 1 if the commander achieves his goal successfully, and 0 otherwise, where i∈S, 1 ≤ j ≤ Fi Maximum time threshold to compromise node k
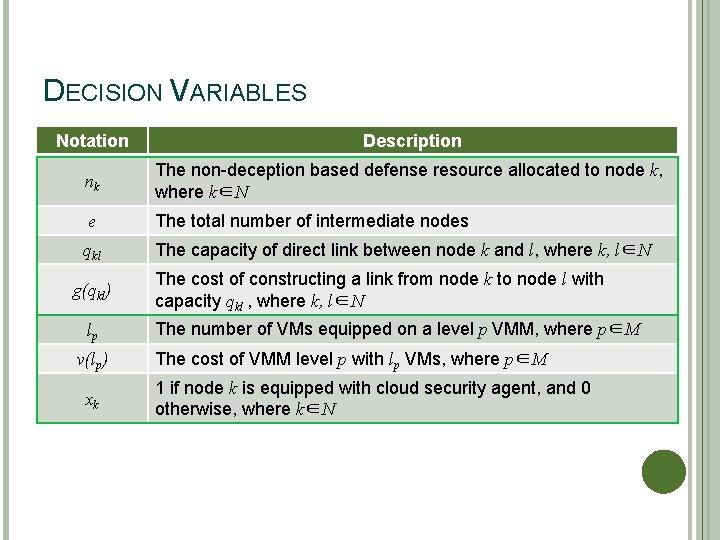
DECISION VARIABLES Notation Description nk The non-deception based defense resource allocated to node k, where k∈N e The total number of intermediate nodes qkl The capacity of direct link between node k and l, where k, l∈N g(qkl) lp v(lp) xk The cost of constructing a link from node k to node l with capacity qkl , where k, l∈N The number of VMs equipped on a level p VMM, where p∈M The cost of VMM level p with lp VMs, where p∈M 1 if node k is equipped with cloud security agent, and 0 otherwise, where k∈N
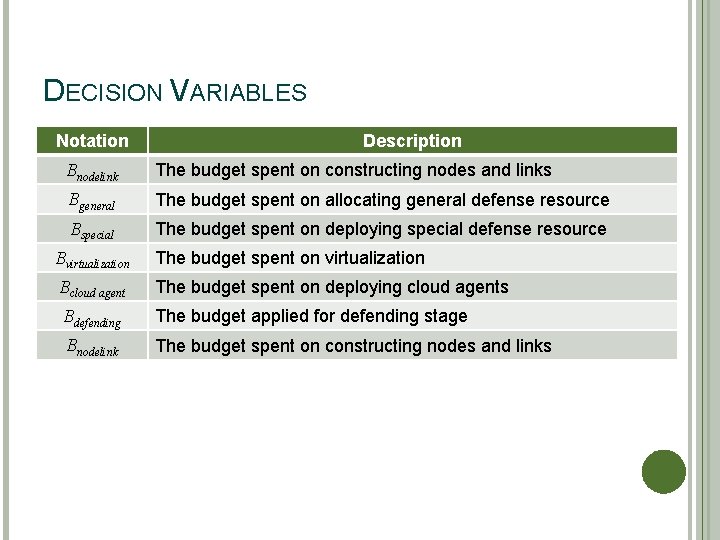
DECISION VARIABLES Notation Description Bnodelink The budget spent on constructing nodes and links Bgeneral The budget spent on allocating general defense resource Bspecial The budget spent on deploying special defense resource Bvirtualization The budget spent on virtualization Bcloud agent The budget spent on deploying cloud agents Bdefending The budget applied for defending stage Bnodelink The budget spent on constructing nodes and links
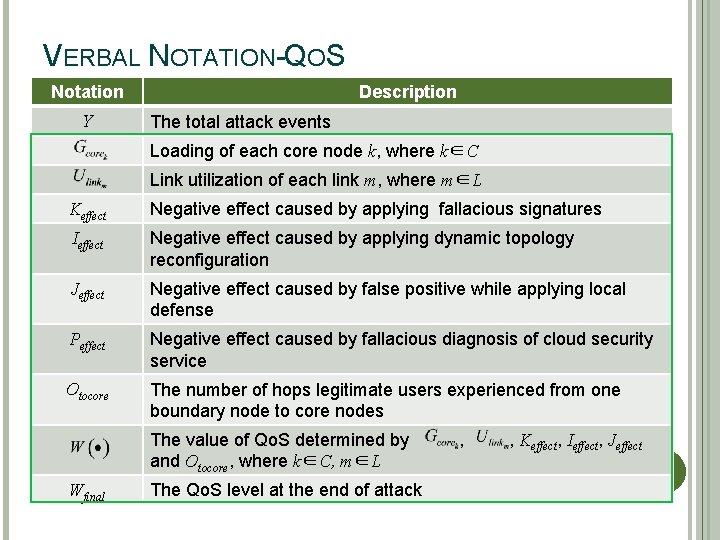
VERBAL NOTATION-QOS Notation Y Description The total attack events Loading of each core node k, where k∈C Link utilization of each link m, where m∈L Keffect Negative effect caused by applying fallacious signatures Ieffect Negative effect caused by applying dynamic topology reconfiguration Jeffect Negative effect caused by false positive while applying local defense Peffect Negative effect caused by fallacious diagnosis of cloud security service Otocore The number of hops legitimate users experienced from one boundary node to core nodes The value of Qo. S determined by and Otocore, where k∈C, m∈L Wfinal The Qo. S level at the end of attack , , Keffect, Ieffect, Jeffect
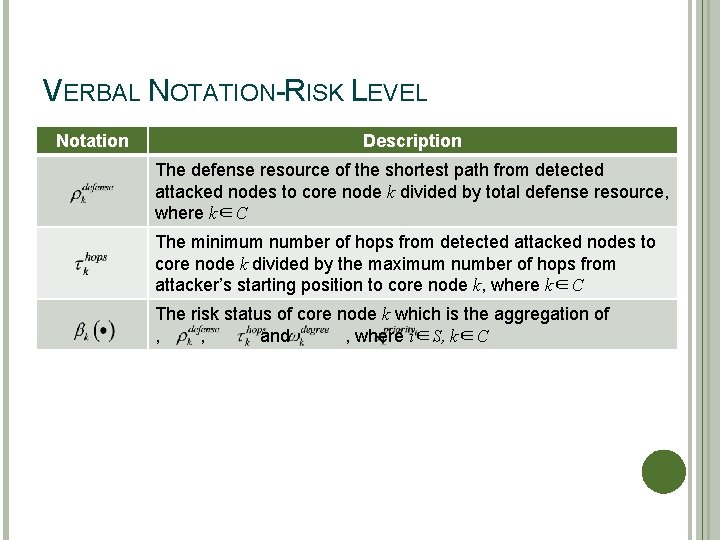
VERBAL NOTATION-RISK LEVEL Notation Description The defense resource of the shortest path from detected attacked nodes to core node k divided by total defense resource, where k∈C The minimum number of hops from detected attacked nodes to core node k divided by the maximum number of hops from attacker's starting position to core node k, where k∈C The risk status of core node k which is the aggregation of , , and , where i∈S, k∈C
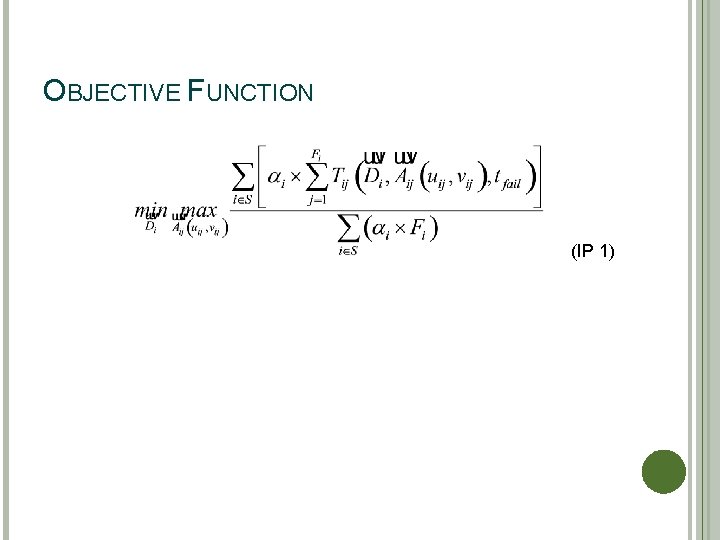
OBJECTIVE FUNCTION (IP 1)
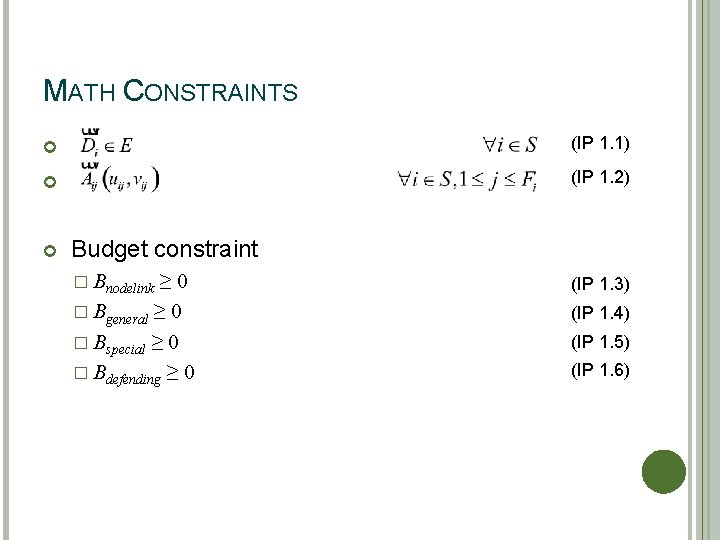
MATH CONSTRAINTS (IP 1. 1) (IP 1. 2) Budget constraint � Bnodelink ≥ 0 � Bgeneral ≥ 0 � Bspecial ≥ 0 � Bdefending ≥ 0 (IP 1. 3) (IP 1. 4) (IP 1. 5) (IP 1. 6)
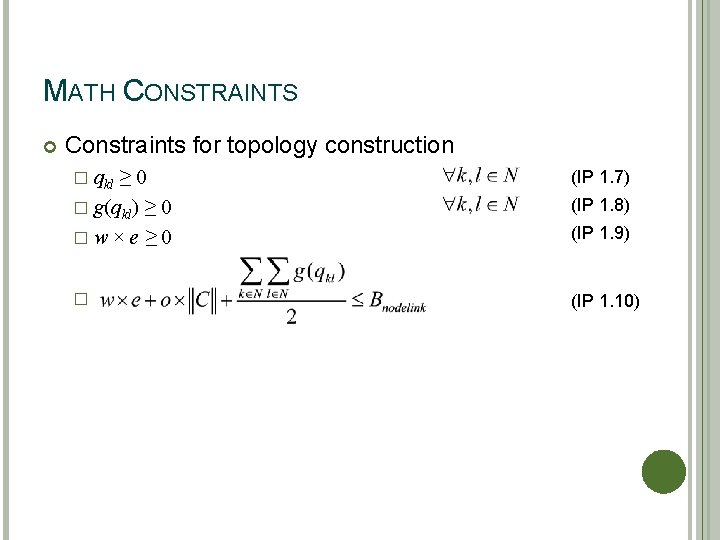
MATH CONSTRAINTS Constraints for topology construction � qkl ≥ 0 � g(qkl) ≥ 0 �w×e≥ 0 (IP 1. 7) � (IP 1. 10) (IP 1. 8) (IP 1. 9)
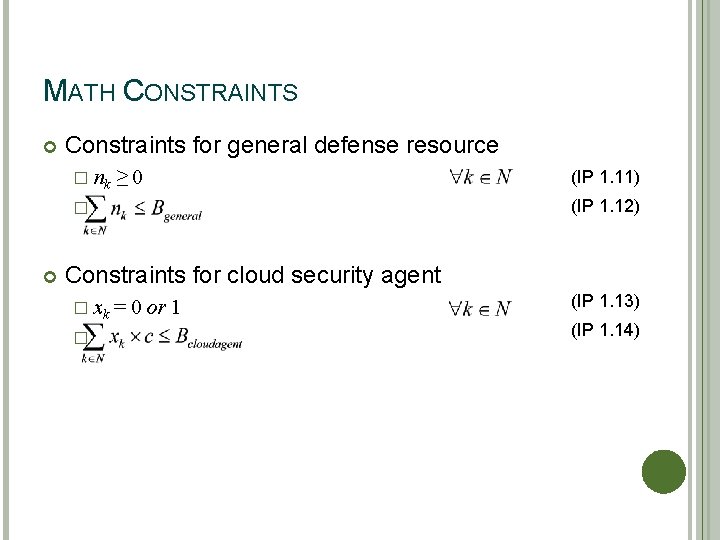
MATH CONSTRAINTS Constraints for general defense resource � nk ≥ 0 (IP 1. 12) � (IP 1. 11) Constraints for cloud security agent � xk � = 0 or 1 (IP 1. 13) (IP 1. 14)
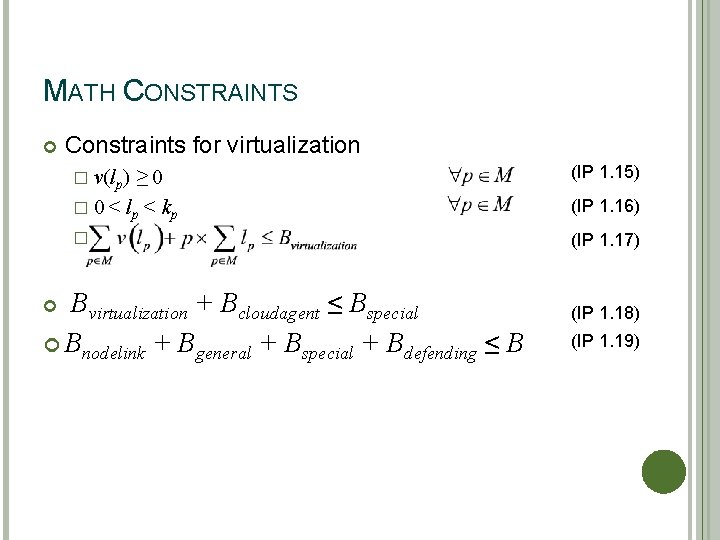
MATH CONSTRAINTS Constraints for virtualization ≥ 0 � 0 < lp < kp (IP 1. 15) � (IP 1. 17) � v(lp) Bvirtualization + Bcloudagent ≤ Bspecial Bnodelink + Bgeneral + Bspecial + Bdefending ≤ B (IP 1. 16) (IP 1. 18) (IP 1. 19)
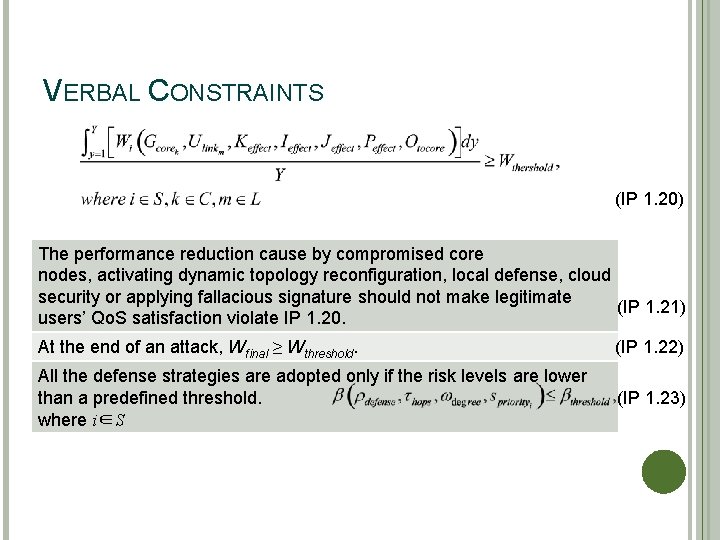
VERBAL CONSTRAINTS (IP 1. 20) The performance reduction cause by compromised core nodes, activating dynamic topology reconfiguration, local defense, cloud security or applying fallacious signature should not make legitimate (IP 1. 21) users' Qo. S satisfaction violate IP 1. 20. At the end of an attack, Wfinal ≥ Wthreshold. (IP 1. 22) All the defense strategies are adopted only if the risk levels are lower than a predefined threshold. where i∈S (IP 1. 23)
THANKS FOR YOUR LISTENING
everinghamwelition.blogspot.com
Source: https://slidetodoc.com/effective-network-planning-and-defending-strategies-to-minimize-3/
0 Response to "Effective Network Defense Strategies to Assure Service Continuity Under Collaborative Attacks Pdf"
Post a Comment